The Problem Nobody Talks About
Most cybersecurity companies lead with fear. “A new ransomware strain is targeting your industry. Is your vendor protecting you?” This messaging is everywhere and frankly, it stopped working. Fear is real in cybersecurity buying decisions, but hammering it repeatedly does not move buyers closer to a purchase. It just creates noise.
The content cybersecurity companies push needs to be structured around education, not alarm. Buyers want to understand protection capabilities, performance benchmarks, and how a vendor actually secures endpoints, devices, and accounts. The studies and visuals are welcome. The fear agenda is not.
There is also a targeting problem
A cybersecurity brand selling into large enterprises is talking to CISOs, CTOs, and internal IT departments who expect depth and sophistication. An MSP targeting small business owners is talking to people who do not have the time, the team, or the appetite for a 3,000-word technical deep dive. These are fundamentally different content jobs and most companies treat them the same way. They repurpose the same message across the same platforms with a different visual and wonder why there is no traction.
Why Cybersecurity Content Fails to Convert
Here is a real example. Picture a graphic from an active cybersecurity vendor targeting SMBs and MSSPs. The design is clean. The numbers are dramatic. 446,646 unknown threats. 7,714 malicious. Zero infections. And the reaction from their target audience is “okay?” Nothing to interact with, nothing to learn, no next step, no incentive to engage.
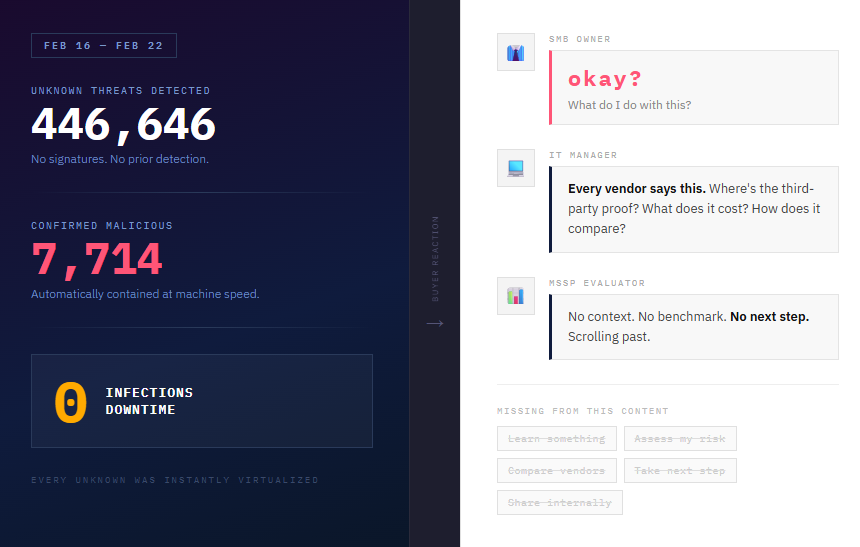
This type of content has been done for years and buyers are so overexposed to it that they look but do not see. It blends into the feed and disappears.
The real problem is not the design, it is the absence of an “aha” moment. Decision makers and the buying community at SMBs, mid-market, and enterprise companies do not need more proof that threats exist. They need help understanding where they stand and what to do about it. An interactive cybersecurity posture assessment, a cost calculator, or even an anonymized before-and-after from an existing client would do more conversion work than any threat counter ever will. Give prospects a way to see themselves in the content and they will engage. Show them someone else’s numbers and they will scroll past.

The ActualTech Media 2025 Cybersecurity Buyers Guide specifically calls out that fear-based marketing does not work and covers what messaging actually resonates with buyers. 55% of buyers said cybersecurity would be a significant focus for them in 2025 FutureB2B, yet the same report flags that everyone says the same things.
According to Demand Gen’s 2025 report, 68% of cybersecurity buyers consume at least three pieces of content before engaging with a vendor Amra & Delma.
Executives are not going to sit through a 20-minute read. They are selective with their time and they gravitate toward content that is high value and quick to consume. The data backs this up, 53.9% of executive content consumption comes in the form of eBooks, cheat sheets, book summaries, and guides. Netline
The Buyer Journey Is Broken — Here Is How to Fix It
Timing is everything and timing is the buying journey. The good news is there are tools today, Clay, 6sense, and AI research tools among them, that let you get remarkably specific about where a prospect actually is:
- When did their contract with their current vendor start?
- What is the equivalent cost of cybersecurity protection for companies of their size and vertical?
- Are they overprotected to the point where employee performance is taking a hit?
- Are they overspending on coverage they do not need at their current scale?
- Are they posting new internal IT or cybersecurity roles, which is often a signal of a gap or a transition?
- What breaches have hit companies in their specific vertical recently that would be directly relevant to their situation?
When you do this research before you create content, you stop broadcasting and start targeting. The difference between content that generates pipeline and content that generates impressions is almost always this: did you put the right message in front of the right person at the right moment in their decision process, or did you post it everywhere and hope?
The content types that actually keep prospects in the funnel and push them toward a decision are specific. Quantified case studies and whitepapers give buyers something to bring to their leadership. Assessment tools and quiz formats let prospects see their own posture, which creates immediate relevance. Third party validation, analyst reports and peer reviews, removes the “of course the vendor says that” objection. ROI and performance calculators hit the financial decision maker directly. Compliance checklists and audit frameworks work well in regulated industries where a prospect needs to justify a purchase internally. Technical deep dives serve the practitioner who will actually implement the solution. And specific security incident post mortems, relevant to their vertical and size, make the risk feel real without resorting to generic fear tactics.
The Content Types That Actually Drive Pipeline
Let me use my own content as a case study here. I wrote a CrowdStrike vs. SentinelOne comparison on this blog and the approach was deliberately different from what most people do when they use AI for vendor research.
Most AI-assisted content in cybersecurity right now follows the same pattern: ask an LLM a question, take the output, publish it. The problem is that LLMs hallucinate, they have training cutoffs, and they have no access to how vendors actually position themselves against each other. The output looks authoritative but often is not.
My process was different
I fed both ChatGPT and Claude Sonnet the official comparison pages from CrowdStrike and SentinelOne directly, so the models were working from primary vendor sources, not their training data. I layered in third party sources, Gartner, Forrester, MITRE ATT&CK evaluations. I ran the same research through both models independently and then cross-checked the outputs against each other. Where they diverged I dug deeper. Where they agreed and cited sources I verified those sources before publishing.
The result is comparison content that holds up because it was built on a foundation of actual research, not AI convenience. That matters for buyers. Comparison content sits right at the vendor shortlist stage of the buying journey, which is one of the highest intent moments in the entire funnel. A buyer reading a CrowdStrike vs. SentinelOne piece is not casually browsing. They are close to a decision. If your content is credible and specific at that moment, it does real conversion work.
Beyond comparison content, the other formats worth investing in are the ones mentioned in the previous section:
- ROI calculators
- Case studies with real numbers
- Third party validated research.
The common thread is that they all give a buyer something concrete to act on or share internally.
How to Use AI to Scale Without Losing Credibility
The biggest misconception about using AI for content is that it is a shortcut. It is not, at least not if you are doing it right.
Where AI genuinely helps is structure. Use it as an outliner to keep your thinking organized and your flow intact. A good outline built with AI assistance will expose gaps in your argument before you waste time writing around them. That is the real value: AI is very good at showing you where your thinking is weak. Let it do that job. Do not let it replace your thinking.
The expertise still has to come from you. The CrowdStrike vs. SentinelOne piece I referenced earlier took weeks to produce properly. The AI handled the research synthesis and the structural framework. I handled the prompt engineering, the source verification, the editorial judgment, and the parts that required actual experience in the field. That combination is what makes the output credible. An LLM with no domain context and no human review layer produces content that looks right and reads smoothly but falls apart the moment a practitioner examines it closely.
The guardrails are not complicated but they are non-negotiable. Every claim needs a source you have actually checked. If two models agree on something, verify it anyway. If they disagree, that disagreement is a signal to dig deeper, not to pick the answer you prefer. And the author needs real experience in the field. AI can synthesize information but it cannot replace the judgment that comes from having actually done the work.
This is not about writing faster. It is about doing deeper, better work with the time you invest.
How to Measure Whether It Is Working
Measurement only works if your tech stack is built to capture it. Most companies track vanity metrics because that is what is easiest to see. Page views, impressions, social reach. None of that tells you whether your content is generating pipeline.
The starting point is knowing where your traffic comes from and which specific pieces of content are driving it. Tools like Snitcher can de-anonymize website visitors and tell you which companies are reading your content and which posts brought them there. That alone changes how you think about what to write next.
From there, the goal is to automate the handoff. Connect your intent and traffic data into your CRM through tools like Apollo and Clay, piped into HubSpot via Zapier, and you stop losing warm signals in spreadsheets. Every meaningful engagement, a prospect reading your comparison post, downloading a whitepaper, completing an assessment, gets captured, scored, and triggers the next relevant content automatically. No engagement is wasted.
When that system is running properly you have an active funnel machine. A prospect who reads your CrowdStrike vs. SentinelOne comparison at the shortlist stage gets served an ROI calculator next. A small business owner who completes a posture assessment gets a relevant case study from their vertical. The content matures them further through the funnel without your sales team having to manually chase every signal.
When presenting this to a CFO or board, skip the content metrics entirely. Show the pipeline. How many identified accounts engaged with content before entering a sales conversation? What was the average deal size of content-influenced opportunities versus cold outreach? What is the cost per pipeline dollar generated compared to your other demand gen channels? Those are the numbers that land.
The Minimum Viable Content Engine for Cybersecurity
If I were starting from scratch tomorrow at a cybersecurity company with a lean team, I would not touch content until two things were done properly. Buyer personas and buyer journeys, built on real data and real research, not assumptions. Most companies skip or rush this step and then wonder why their content calendar produces activity but not pipeline. Get this foundation right first and everything that follows gets easier.
Once both are ready I would map content sets to each journey segment with the right content type for each stage, managed within a calendar that includes a deliberate repurpose plan. Not repurposing as in posting the same graphic with a different color, but structuring each core piece so it can live in multiple formats across multiple channels without losing its relevance.
For production I would hire analysts and subject matter experts, outsourcing is perfectly fine here, and pair them with the AI-assisted research methodology I outlined in this article. The expertise has to be real. The process can be efficient.
For distribution I would invest in PR, technical LLMO optimization, and cold and warm outbound channels where you can put the right content directly in front of the right persona at the right moment in their journey.
If you want a quick headstart, you are welcome to use my Cybersecurity Content Strategy Template.
What I would skip entirely is traditional SEO content built around generic search volume. Writing another “what is ransomware” post to chase keywords that your total addressable market either already knows the answer to or will never act on is a waste of time, budget, and credibility. Your TAM and SAM (Servicable Addressable Market) do not need to be scared. They need to be helped. Build content that does that and the pipeline will follow.
0 Comments